Strategic Cybersecurity Leadership You Can Trust
Cybersecurity shouldn’t be complicated, expensive, or out of reach for growing businesses. That’s why TrustedCISO exists – to make enterprise-level security expertise accessible to the companies that need it most.
How TrustedCISO Started
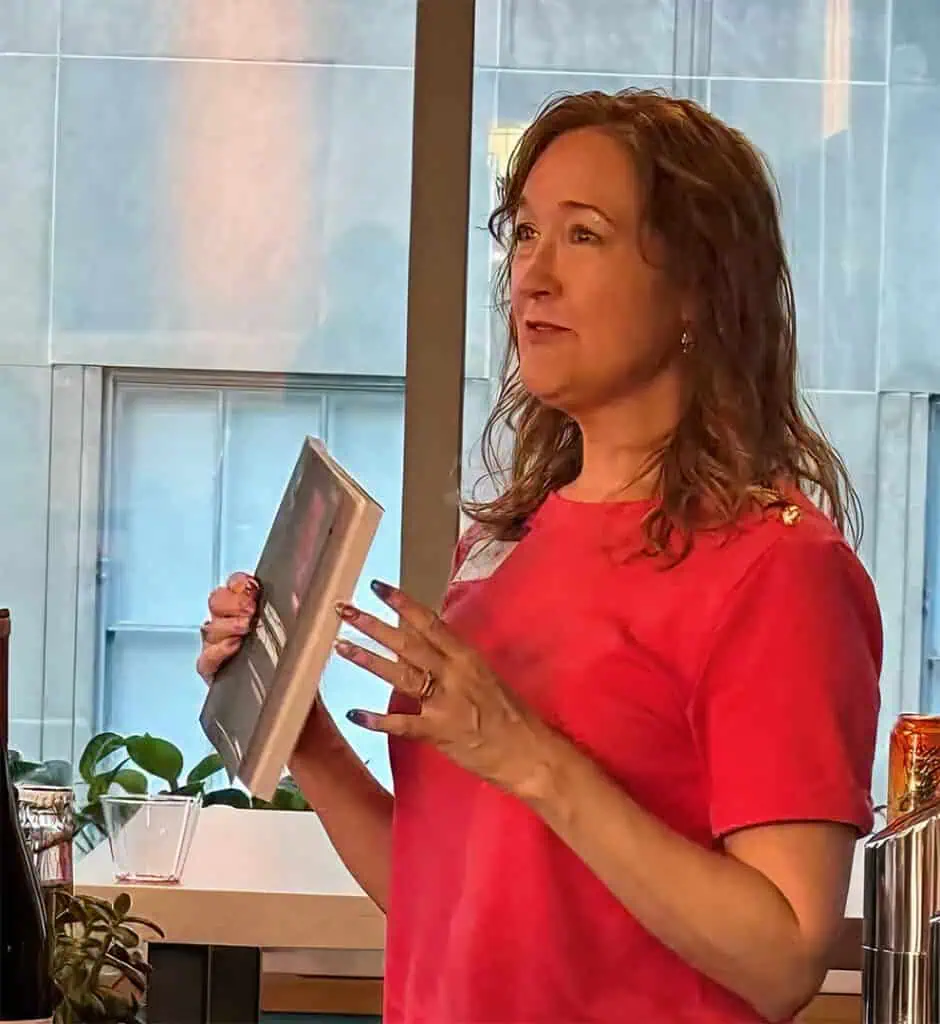
Debra Baker didn’t set out to start a cybersecurity consulting firm. She was building a successful career as a CISO.
Her path to cybersecurity began in the late 1990s as a network engineer in the U.S. Air Force. After her military service, she joined IBM and then moved to Cisco, where she transitioned fully into the security space. She spent years at Entrust DataCard working on PKI (public key infrastructure) integration, then became CISO at RedSeal Networks, where she successfully led the company through SOC 2 Type 1 and Type 2 certification.
But something was changing in the market. Virtual CISO services were emerging as an alternative to full-time security leadership. Debra saw an opportunity – and a problem.
Small and mid-sized companies needed the same level of security expertise as large enterprises, but they couldn’t justify a $200K+ CISO salary. Many were turning to premium consulting firms charging $300-500 per hour, putting compliance out of reach. Others were trying DIY approaches with tools like Vanta and Drata, only to realize they needed expert guidance.
So Debra founded TrustedCISO to bridge that gap. The mission was simple: provide the same caliber of security leadership she delivered as a CISO, but at a price point that made sense for growing businesses.
Eight years later, that mission hasn’t changed.
Our Core Values
Transparency
You’ll never wonder where your money is going or why we’re recommending something. We provide clear pricing upfront and explain every decision in plain English – not security jargon.
Accessibility
Enterprise-level security shouldn’t be reserved for enterprises. We make expert guidance available to companies at every stage of growth, with pricing that reflects real-world budgets.
Expertise
With over 30 years of experience across government, enterprise, and SaaS environments, we’ve seen what works and what doesn’t. We bring that knowledge to every engagement.
Personalized Service
Unlike larger firms that match you with whoever’s available, you work directly with our founder and team. No cookie-cutter approaches. No rotating consultants. Just focused attention on your specific needs.
Military Discipline
As a Veteran-Owned business, we bring the same level of discipline, integrity, and dedication to your security program that you’d expect from military service.
Founder & Leadership

Debra brings over 30 years of cybersecurity expertise to every client engagement. She holds two of the industry’s most respected certifications – CISSP (Certified Information Systems Security Professional) and CCSP (Certified Cloud Security Professional) – and served as a Distinguished Subject Matter Expert for ISC2’s CCSP exam development, helping shape the certification standard itself.
She’s the author of A CISO Guide to Cyber Resilience, which was inducted into the Cybersecurity Canon by Palo Alto Networks and is now used in graduate cybersecurity programs at East Carolina University. The book has been recognized as one of the Top 10 Security Books by Help Net Security.
Beyond consulting, Debra is an active thought leader in the cybersecurity community. She hosts the CISO Guide to Cyber Resilience Podcast, speaks at industry events, and contributes to publications like Cyber Defense Magazine. She’s been recognized as one of the Top 100 Women in Cybersecurity and was named “Recognised Leader for Cybersecurity Solutions 2017 – Technology Elite.”
Debra holds an MIT Sloan School of Management education and is the inventor on a provisional patent for CompliBot AI, an AI-driven vendor assessment tool. She also founded Crypto Done Right, a separate cybersecurity initiative focused on cryptographic best practices.
Our Team

Prasidy Ochi serves as Chief of Staff at TrustedCISO, working closely with the CEO to drive strategic initiatives, support daily operations, and help align the business for growth. In this role, Prasidy collaborates across marketing, sales, and cybersecurity service delivery, ensuring seamless execution and continuous improvement.
Prasidy holds a bachelor’s degree in Political Science and International Relations from Syracuse University and is currently pursuing an MBA with a concentration in Cybersecurity at UNC Greensboro. Committed to expanding technical expertise, Prasidy is also enrolled in the Sentinel Cybersecurity Bootcamp, gaining practical experience in threat analysis, compliance, and security operations.
With a strong focus on governance, risk, and compliance (GRC), Prasidy is passionate about bridging cybersecurity, business strategy, and organizational leadership. Her goal is to help clients strengthen digital resilience and empower the team to deliver outstanding results in a fast-changing environment.

Jace Nguyen is an accomplished professional with more than 15 years of experience in management, sales, and customer service. As the owner and operator of several successful ventures, Jace developed a strong foundation in business operations, cost management, and team leadership. His ability to drive performance through efficient processes and exceptional customer engagement has been a hallmark of his success.
In addition to his entrepreneurial achievements, Jace is a licensed North Carolina Real Estate Broker, representing clients in residential transactions with professionalism and integrity. His diverse background provides a unique perspective on risk management, client relations, and operational strategy—skills that translate naturally into the world of cybersecurity.
Advisory Board

Ex-big 4 and experienced Information Security Investigator and Technologist with a deep technical understanding of the Managed Security Services (MSS) technologies, TS/SCI Network Security, Vulnerability Detection, incident Response, Internal and external Threat and Hunt Operations, intrusion analysis, anomalous behavior analysis, and threat intelligence through Survey, Secure and Protect Methodologies.

Cyber-Security Expert and Researcher with broad expertise across the domain including network security, applied cryptography, malware defenses, and defensive architectures. I also teach network security as an adjunct faculty at the University of Texas at Austin. Author of 2 Python books.
A seasoned expert in security, compliance, and IT risk advisory services, with over two decades of experience helping organizations enhance their security and compliance frameworks. My mission is to provide comprehensive, tailored solutions that not only meet regulatory standards but also strengthen the overall security posture of your business.
What Makes TrustedCISO Different
No Random Consultant Matchmaking
Ever been matched with a consultant who barely knows your business? We don’t do that. When you work with TrustedCISO, you work directly with Debra – not whoever happens to be available that week. You get 30 years of hands-on experience, not a generic playbook.
We Have Skin in the Game
Our 100% first-attempt audit pass rate isn’t an accident. It’s what happens when you prepare clients thoroughly instead of cutting corners. Every audit reflects on our reputation, so we treat your security program like it’s our own.
Transparent Pricing That Actually Saves You Money
Most vCISO firms hide their rates behind “request a quote” forms. We don’t. Our $175/hour rate is right there on the website – and it’s 40-65% less than what premium competitors charge. We also offer transparent monthly packages, so you know exactly what you’re investing before we start.
Federal Contracting Doors We Can Open
As a Veteran-Owned Small Business (VOSB), Woman-Owned Small Business (WOSB), and Economically Disadvantaged Woman-Owned Small Business (EDWOSB), we bring unique advantages to clients pursuing government contracts. Need CMMC certification for defense work? We’ve been there.
Thought Leadership That’s Actually Used
Debra’s book, A CISO Guide to Cyber Resilience, isn’t sitting on a shelf collecting dust. It’s been adopted in university cybersecurity programs and inducted into the prestigious Cybersecurity Canon. This isn’t just theory – it’s a roadmap built from decades of real-world experience.
Credentials & Recognition
These aren’t just credentials – they’re proof of expertise earned over three decades